Strengthen SOC 2 compliance through controlled, auditable reporting
Give Compliance and Security teams a structured way to manage sensitive reports in line with SOC 2 trust principles, helping reduce audit friction and strengthen trust.




Trusted by +300 leading
organisations worldwide









.svg%20(1).avif)








.webp)
.webp)
.webp)




.svg%20(1).avif)








.webp)
.webp)
.webp)




.svg%20(1).avif)








.webp)
.webp)
.webp)




.svg%20(1).avif)








.webp)
.webp)
.webp)




.svg%20(1).avif)








.webp)
.webp)
.webp)


Why SOC 2 compliance breaks down in practice



Bring structure and evidence to SOC 2 reporting


Designed to support SOC 2 compliance

Meet SOC 2 Trust Services Criteria
Support SOC 2 requirements across Security, Availability, Confidentiality and Processing Integrity through controlled reporting and documented processes.

Enforce access control and accountability
Apply role-based access, case-level permissions and authentication controls aligned with SOC 2 CC6 (Logical Access Controls).

Maintain complete audit trails
Automatically log actions, access and changes to support SOC 2 CC7 and CC8 evidence requirements.

Support SOC 2 Type II audit readiness
Provide continuous traceability and historical evidence to demonstrate control effectiveness over time during Type II audit periods.
Key capabilities
that support SOC 2 compliance

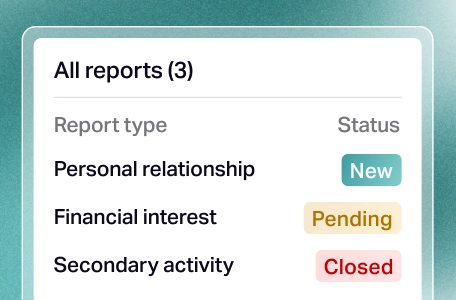
Controlled intake of sensitive reports
Centralise security, compliance and ethics-related reports in a single system with structured forms and consistent data capture.

Role-based access and segregation of duties
Enforce least-privilege access with role-based and case-level permissions aligned with SOC 2 logical access controls.

Audit-ready logs and traceability
Automatically record actions, access, decisions and changes to support continuous evidence collection for audits.

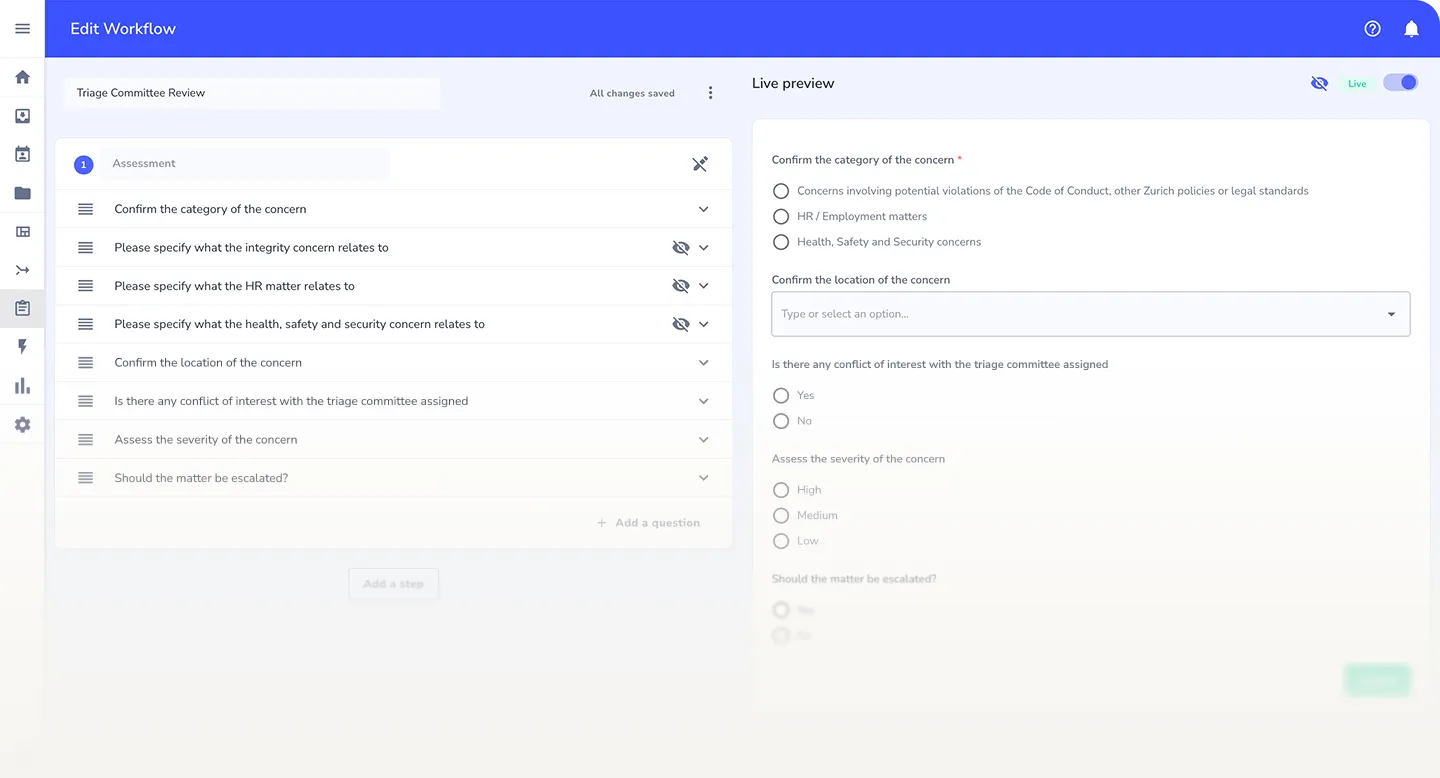
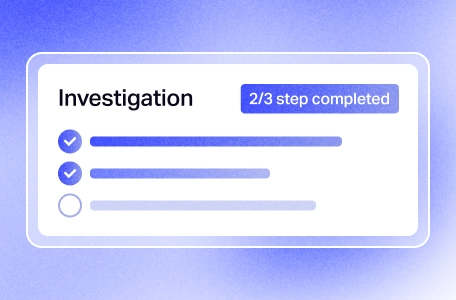
Standardised workflows and approvals
Apply consistent handling, investigation steps and approvals to demonstrate repeatable, operating controls over time.
%202.svg)
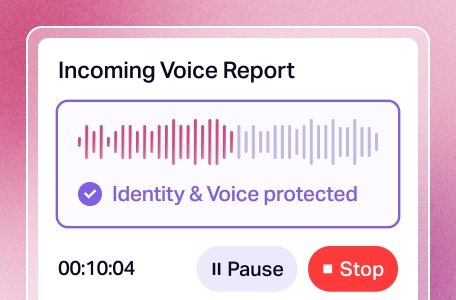
Secure communication and data handling
Protect sensitive information with encryption, controlled visibility and secure follow-up, supporting confidentiality requirements.

Evidence export for audits
Generate logs, reports and documentation to support SOC 2 audit requests without manual reconstruction.
Outcomes organisations achieve with Whispli for SOC 2
Reduced audit friction
Evidence is continuously collected and structured, limiting last-minute requests, manual reconstruction and audit stress.
Stronger control defensibility
Clear audit trails, access logs and documented actions help demonstrate that controls are not only defined, but operating effectively over time.
Lower operational overhead for compliance teams
Standardised workflows and automated logging reduce manual work while maintaining a high level of control and oversight.
Empowering global organisations with higher engagement and stronger compliance outcomes
More than 300 companies, organisations and education institutions rely on Whispli to run their global speak up programs.
Whispli has been deployed in over 60 countries, demonstrating its flexibility and ease of configuration.
With no language barriers, Whispli empowers everyone to speak up confidently.
Modernise your global compliance strategy
Move from fragmented reporting tools to a single system of record designed for the realities of 2026.
Talk to our compliance experts and strengthen your global governance while uncovering risks before they escalate.

Explore more resources
Frequently asked questions
Whispli provides controlled reporting workflows, strict access management and complete audit trails. All actions related to sensitive reports are documented and traceable, supporting SOC 2 Trust Services Criteria.
Whispli maintains continuous logs, timestamped actions and historical records, allowing auditors to verify that controls operate consistently over time, not just in design.
Access is managed through role-based and case-level permissions, SSO and two-factor authentication. All access and actions are automatically logged, supporting SOC 2 logical access and monitoring controls.
Yes. By centralising reports, decisions and evidence in one system, Whispli reduces manual evidence gathering and helps teams respond faster and more confidently during SOC 2 audits.










.webp)

.webp)
.webp)


.avif)




%201.avif)
%201%20(2).avif)
%201%20(1).avif)
